Featured News
Garrett News Hub
Garrett Inaugurates Wuhan Innovation Center to Advance Zero-Emission Mobility
Garrett opens second innovation center in China to expand zero-emission R&D capabilities New Wuhan lab prioritizes high-speed E-Powertrain systems for zero-emission applications Wuhan and Shanghai…
Garrett’s Nils Martens named one of Automotive News Europe’s 2025 Rising Stars
At Garrett, we believe progress comes from bold ideas, strong teams, and the leaders who bring them together. Today, we’re proud to celebrate Nils Martens,…
Creating a meaningful impact: Garrett 2024 Sustainability Report
Garrett Motion has released its 2024 Sustainability Report, highlighting how the company created meaningful impact across environment, social and governance throughout the year. Garrett continues…
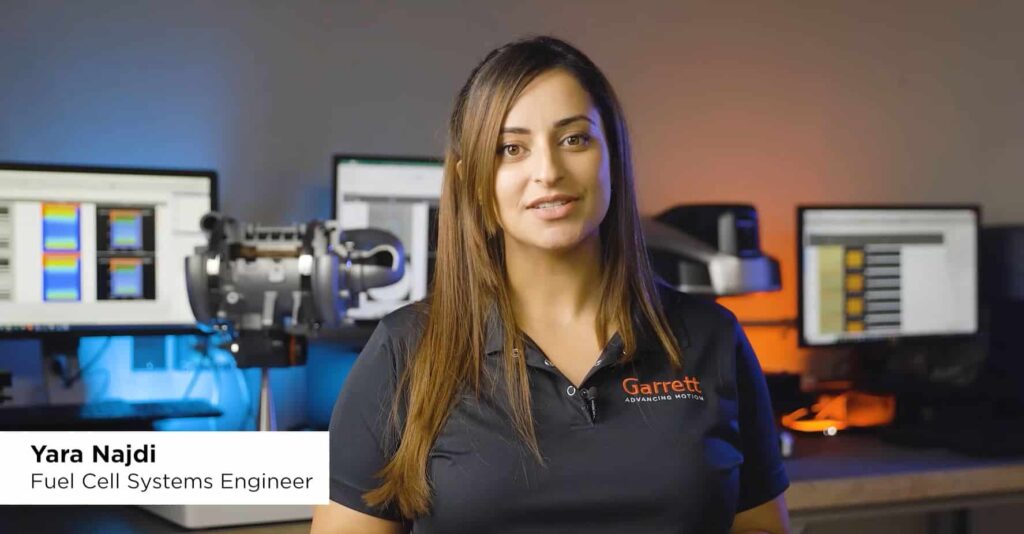
Advancing Zero-Emission Heavy-Duty Vehicles: Garrett’s Role in the BeBoP Fuel Cell Project
The push for zero-emission heavy-duty transport is accelerating, and hydrogen fuel cells are emerging as a game-changer. At the forefront of this transition is the…
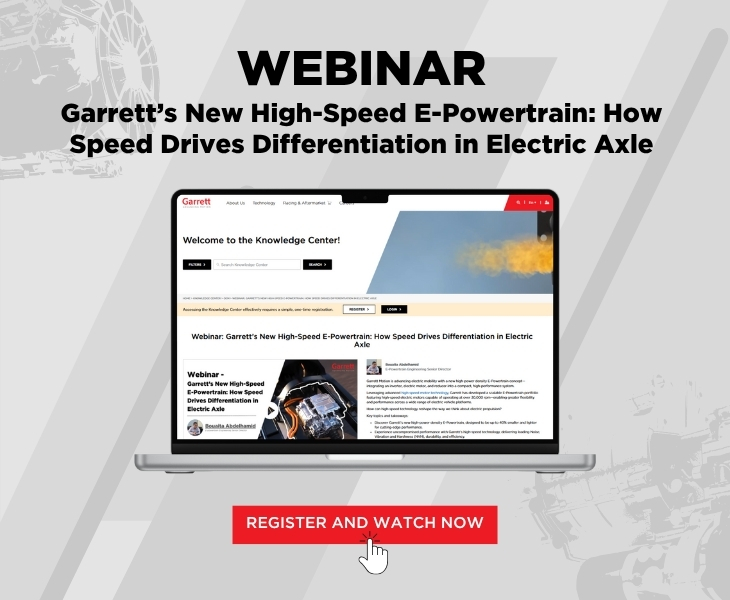
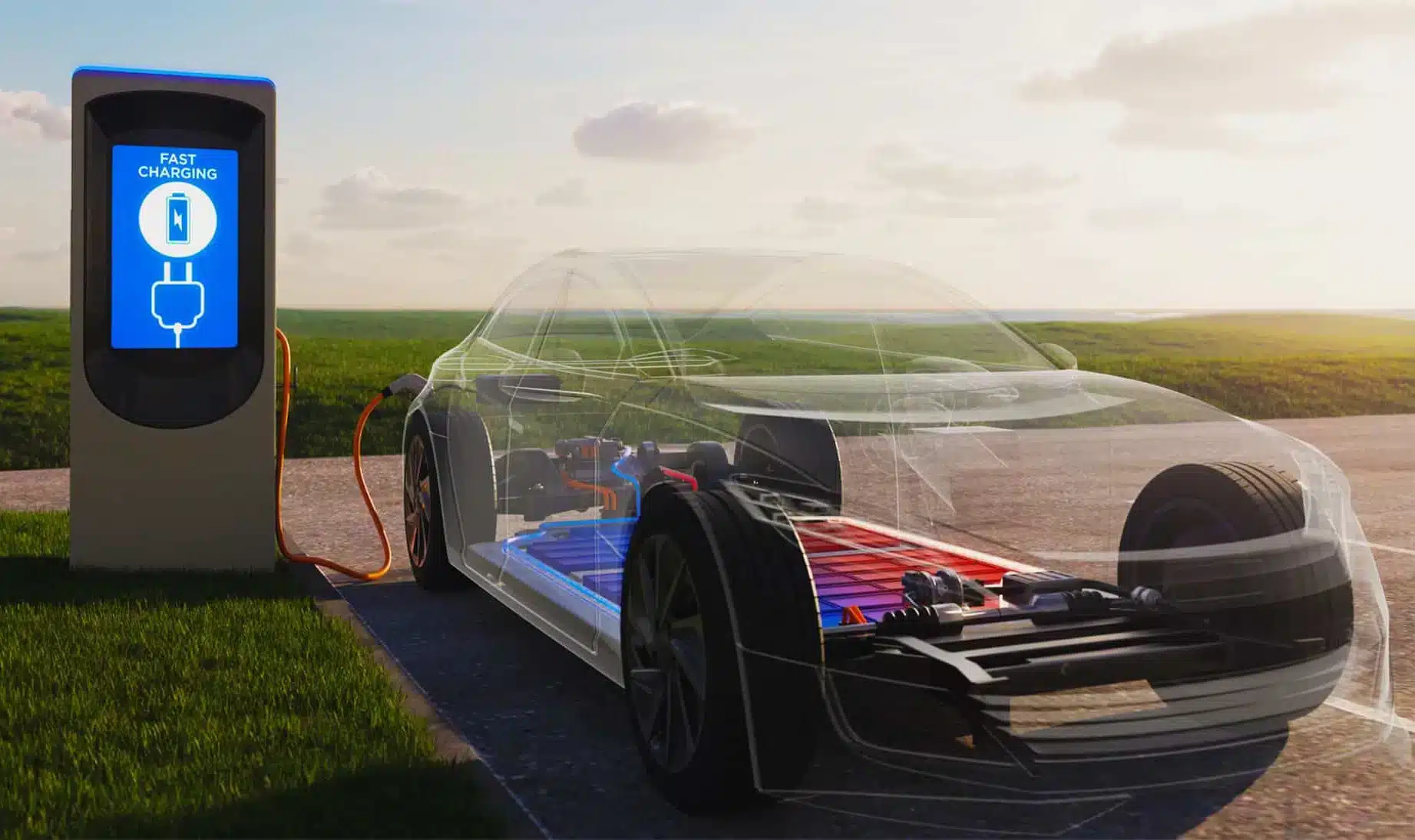
Garrett’s High-Speed, High-Power Density E-Powertrain Advances the Future of Motion
In the fast-changing world of electric vehicle (EV) technology, Garrett has once again demonstrated its expertise by unveiling a revolutionary high-speed, high-power density Electric Powertrain….
Garrett and HanDe Sign Strategic Partnership Including Series Production Award to Accelerate Electrification of Heavy-Duty Trucks with Advanced E-Axle Systems
ROLLE, Switzerland and PLYMOUTH, Mich., April 23, 2025—Garrett Motion Inc. (NASDAQ: GTX), a leading differentiated automotive technology provider and Shaanxi Hande Axle Co., Ltd. (HanDe),…
Advancing Motion: Garrett Presents Breakthrough Electrification and Turbocharging Innovations at Auto Shanghai 2025
• First public showcase in China of 3-in-1 E-Powertrain and E-Cooling Compressor technologies, advancing zero-emission vehicle performance • Differentiated turbocharging solutions for passenger and commercial…
Thermal Management for EV/HEV 2025
On February 27th 2025 in Munich-Germany, Garrett Motion will be present at Thermal Management for EV/HEV 2025, one of the longest-running events in this field of expertiese. This year edition’s will focus on five key industry drivers: cost-competitiveness, ultra-high thermal system efficiency, vehicle efficiency and reliability, energy efficiency with longer driving cycles, and improved vehicle autonomy.
26 Years in a Row Powering Champions at Le Mans 24h
Le Mans isn’t just a race — it’s an exhilarating 24-hour challenge where only the most advanced machines survive! For nearly a century, it has…
Turbo Training 2025: Garrett Motion Korea Hosts Aftermarket Tech-Day in Bangkok
Garrett Motion Korea hosted its 2025 Tech-Day in Bangkok, offering hands-on turbo training, launching an updated product catalog, and showcasing electric boosting solutions for zero-emission goals.
Turbo Talk and Drift Action: Garrett Powers Through a Wet Weekend at RoDrift Bucharest
Despite the rain, RoDrift 2025 roared in Bucharest as Garrett showcased turbo innovation and powered top drifters in Romania’s premier drift event.
A Strategic Roadmap for Indian Aftermarket Success
Garrett India has unveiled a strategic plan to propel Aftermarket growth across India, Nepal, Bangladesh and Sri Lanka, providing Master Distributors in each country with a roadmap leading to mutual success.

Follow Us
Technology Highlights
Redefining zero-emission automotive technologies
Increasingly stringent CO2 emissions and the need to reduce dependency on fossil fuels are quickly creating demand for alternative sources of energy. Garrett Motion’s growing...
Garrett E-Turbo: Ready Today to Meet & Exceed the Industry’s Electric Boosting Needs
Garrett’s award-winning E-Turbo is ready today to meet and exceed the industry’s electrification-boosting needs. The result of unparalleled engineering expertise and advanced electric capabilities, Garrett’s...